Are you currently running an online business or planning to launch one soon? If so, addressing potential information security risks should be your top priority.
Many retailers use multiple systems, each implemented and developed by different companies. While this can aid business with development, it also increases the risk of personal data leaks and may harm project availability. Our company’s experts advise: pay attention to your online store’s security by adhering to secure development standards.
Cyber threats in eCommerce
Hacking an online store involves unauthorized access to its data or functions with the aim of changing, stealing, or damaging them. A hacker identifies a vulnerability in the software (often called a “security hole”) and exploits it to compromise the program’s integrity.
Attackers may have various reasons, including financial fraud, blackmail, spreading viruses, political revolt, gathering data for competitors, or even simply for entertainment — newbie hackers often practice on real projects. In eCommerce, the most common types of cybercrime include:
SQL injection
SQL injection involves injecting arbitrary SQL codes into application queries to a database. If successful, the attacker can view and copy local files, execute commands on the server, or download user data, including credit card numbers and passwords.
A hacker can carefully create a backdoor into an organization’s system and remain undetected for a long time.
XSS attack
XSS (Cross-Site Scripting) is a common vulnerability found in many web applications. The attacker injects code into the website that wasn’t intended by the developers, and this code executes whenever users visit the page.
Hackers use XSS to hack into customers’ personal accounts or redirect them to fake pages. These fake pages, like clones of an online store, bank, or payment system, trick users into entering confidential data, which the hacker then steals.
DDoS attack
A DDoS (Distributed Denial of Service) attack floods a server or network with a massive amount of traffic from many computers or devices. The system can’t handle this overload, causing the website to crash.
The goal of a DDoS attack is to disrupt the website’s normal functioning to damage your business. Hackers often demand ransom from online store owners, threatening to continue the attack if not paid.
Viruses
Viruses are pieces of code placed on a website’s pages to infect visitors’ computers with malware. Once inside a device, the virus can encrypt files, intercept data, or block access to systems.
Malicious bots
Malicious bots account for 30% of online traffic and can freeze or crash an online store. These bots mimic real users by browsing products and adding them to carts but don’t complete transactions. Real buyers may see items as out of stock due to bot activity.
The behavior of bots is somewhat reminiscent of a DDoS attack, but unlike the latter, bots do not “attack” the infrastructure, but imitate the activity of real users and thus create problems with order processing.
Man in the middle (MITM) attack
In a MITM attack, a hacker intercepts communication between users. They may passively eavesdrop to steal information or actively pose as a bank, online store, or trusted contact to deceive users. Incorporating tools like Microsoft Entra ID, which provides secure identity management and safeguards user communications, can significantly reduce the risk of such attacks. Hackers use MITM attacks for competitive intelligence, account intrusion, or financial fraud.
Skimming
Skimming involves placing malicious code on a store’s checkout page to steal credit card and payment information during checkout. This code is hard to detect and doesn’t show obvious signs of cyber fraud.
These are just some common website hacking methods. There are others, more complex and sophisticated, each requiring varying time and resources. However, they all lead to serious financial and reputational losses.
So how do you protect yourself? We recommend using a reliable CMS, a hosting solution with security monitoring, and conducting regular code reviews. Now, let’s get into detail.
Choosing a solid CMS
First, let us remind you that a CMS (Content Management System) is software used to create, fill out, and manage websites. It serves as the foundation or “engine” of a website.
Like any large-scale software, CMSs have vulnerabilities that hackers can exploit to get access to a website. These vulnerabilities often lead to serious e-commerce security threats. No platform can guarantee 100% security because websites are constantly changing due to updates and integrations with external systems. However, when choosing a CMS for your online store, look for those with:
- A large developer community
- Regular and planned releases of new versions
- A strong technical team dedicated to quality and product promotion.
Read our article eCommerce Software Development: Platforms, Features And FAQs to learn how to choose a CMS for a successful online store.
What is safe: a ready-made CMS or a custom one?
For an eCommerce project, you can either develop a platform from scratch (using PHP or frameworks like Laravel for example), or use a ready-made solution.
While a custom platform may seem more secure because its code is unique, as a business owner, you should consider whether the development team can regularly update the CMS. This is vital because updates are essential for improving the reliability and security of the project, making it more resistant to new malware that emerges almost daily.
On the other hand, ready-made CMSs receive regular updates from their developers. Information about new versions is usually available directly in the admin panel. Regular updates and patch management process is key to eCommerce security. They quickly address vulnerabilities, reduce risks, and prevent hackers from exploiting gaps, protecting system integrity and user data.
Product companies also actively monitor for vulnerabilities. If any are discovered, they promptly inform customers and provide instructions on what to do next. For example, the CS-Cart eCommerce platform has a forum where experts announce such events and where you can download updated CMS versions or security patches.
Read more: Why eCommerce Websites Require Project Maintenance After Release?
What is safe: an open source or proprietary CMS?
Every application is made up of code, initially open and accessible to anyone, but access can be restricted if needed, making it a closed-source or proprietary platform.
Open code has its pros and cons. Hackers can closely analyze it to find vulnerabilities, but it’s also scrutinized by a community of professional developers aiming to detect and fix bugs before attackers exploit them. Therefore, for data security, it’s best to choose a ready-made open-source CMS. One such option is CS-Cart, a platform for launching online stores and marketplaces, used by over 35,000 eCommerce projects in 170 countries.
With a closed system, the customer relies entirely on the service provider to detect, develop, and release patches to fix vulnerabilities. The customer and their technical team can’t participate in this process due to lack of access to the code.
Code review
A code review involves inspecting code for potential vulnerabilities, cleanliness, and adherence to platform standards. It’s done by specialists like technical leads, team leads, and experienced developers.
Let’s focus on code clarity. This refers to its simplicity, and modularity. How does this affect security? Directly. Clear logic and structure, visible fields, identifiers, and timestamps make it easier to find potential or actual data leaks. On the other hand, finding flaws in messy code requires a long, painstaking analysis. And during a hacker attack, time is critical.
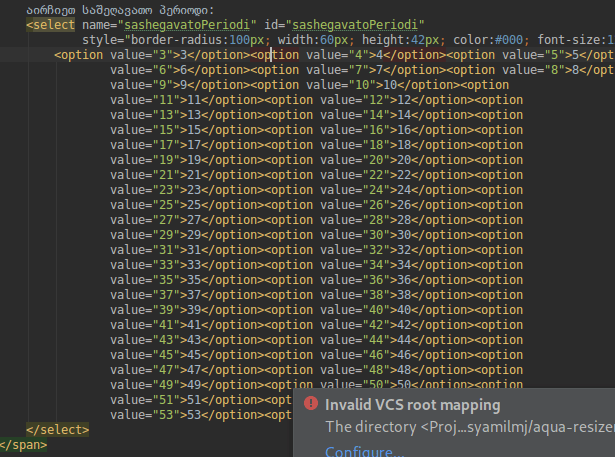
Dirty code example
At Simtech Development, after reviewing the code, we provide clients with a report of the issues we’ve found. This includes possible vulnerabilities, performance issues, compatibility with third-party modules, and ease or complexity of updates.
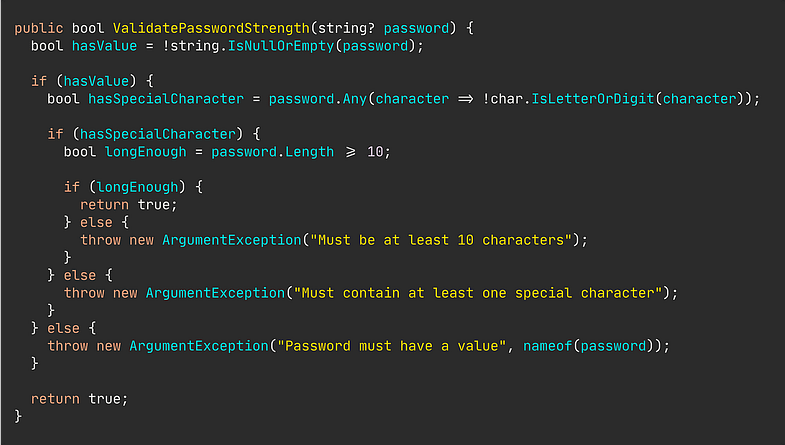
Clean code example
To sum it up, we’ll emphasize once again: code review helps to easily identify accidentally or deliberately left holes in the code that provoke the threat of data leakage. Therefore, our advice is to carry out such checks regularly.
Read more: How We Perform A Website Audit And Code Review
Hosting solution customized for eCommerce
The hosting provider also bears responsibility for the security of an online store. A responsible provider takes necessary measures to protect their own and client data. They install filters, firewalls, and systems to detect malicious attacks. They monitor traffic and watch for suspicious activity, promptly blocking requests from potentially dangerous sources.
When considering a hosting provider, aside from quality services, they should offer prompt technical support and be available 24/7. Ideally, they should specialize in eCommerce, allowing to offer solutions tailored to specific online store platforms.
Tips to keep your online store data secure
To sum it up, we would like to list the main recommendations for ensuring data security on an eCommerce site. Some of them will seem trivial to you, but in matters of information security there are no trifles:
- Update the platform regularly.
- Ask an IT specialist to hide the type and version of the installed CMS and its plugins; do not reveal them in the page code.
- Avoid using counterfeit versions of CMS, as they may deliberately reduce security or contain malware.
- Use strong passwords for administrator and user accounts.
- Ensure your email security by properly configuring authentication protocols to prevent spoofing and phishing attacks as well. Use an SPF record generator to create and implement accurate SPF records for your domain.
- Put planning, project management, and monitoring systems behind a VPN, such as VPN Surfshark.
- Ensure personalized access. This can discourage potential data leaks, even from within your own company.
- Avoid using the same passwords for different websites.
- Do not share passwords in public chats; use open source password managers instead.
- Use two-factor authentication whenever possible.
- Encrypt data transferred between your server and visitors’ browsers.
- Apply filters and check all data received from site visitors. Do not blindly trust information entered into forms or sent through requests.
- Backup your online store data regularly. Store copies on separate media or a cloud service.
Overall, it’s important to focus not just on following rules, but on cultivating a culture of conscious safety within your company. Adhering to these basic measures should become a standard practice, ensuring the protection of your online store.
Conclusion
eCommerce is rapidly growing, attracting significant investments and millions of users. However, this growth also makes online stores and marketplaces prime targets for cybercriminals.
Each year, cybercriminals develop more sophisticated methods of attack. Fortunately, there are tools available to combat these threats. If you’re concerned about the security of your project, reach out to us: the Simtech Development team will help you choose a reliable CMS, seamlessly upgrade from outdated website software, review your code, and host your website on a hosting solution tailored to eCommerce requirements.
